Introduction
Risk register is a significant constituent of the risk management framework on the whole. In fact, risk register allows defining possible risks that can be potentially dangerous for the project. Thus, it provides opportunities for risks prevention because project developers will be able to prevent the possible risks or at least minimize their negative effect. One of the possible ways to define the risks and develop a risk register is a risk workshop. As a rule, it is a meeting that unites the stakeholders in order to review the project and elicit the questions to be answered or issues to be explained that can become risk factors in the process of project implementation. Every workshop will be specific due to the particular project objectives, but still each of them is supposed to include three stages (Danesh-Mand, 2015). These stages are a pre-risk workshop that comprises preparatory activities, a risk workshop itself, and a post risk workshop, which presupposes the development of a risk register.
Pre-Workshop Activities
Pre-workshop activities make a significant preparatory process that is crucial for the workshop functioning. Proper preparation contributes to the success of a workshop. Thus, it is important to define the participants of the risk workshop. To empower the risk identification process, it is advisable to involve representatives of all project’s stakeholders. As a rule, the project manager decides on the participants. However, project sponsors are also frequently involved. All key stakeholders should participate in a risk workshop “to review existing risks and identify and assess new risks, resulting in an update to the Risk Register” (Hillson & Simon, 2012, p. 69).
Hillson and Simon (2012) also agree that an efficient workshop includes from 10 to 16 participants. However, it is better to have more people at a workshop than having too little. In the case of Flayton Electronics, the participants of the workshop will include the company’s CEO, vice-presidents, security manager, bank representative, chief managers from every of the six states where Flayton Electronics shops function, and the head of the customer service.
Secondly, it is necessary to plan the duration of a risk workshop. Such workshop commonly lasts from one to three days (Hillson & Simon, 2012). Every day should be carefully planned. Thus, risk workshop agenda is developed to cover every activity that is going to happen during the workshop. The agenda should be created in advance of the workshop to allow the invited stakeholders to plan their participation and prepare for the meeting. The risk workshop agenda can include some documents, for example, project summary. Moreover, the invited participants can provide some lists of the possible risks to be discussed during the workshop.
Risk Workshop Agenda
The risk workshop for Flayton Electronics is going to last for two days. According to Hillson and Simon (2012, “a formal two-day risk workshop is used to identify project risks as well as to assess their probability and impacts against predefined scales as set out in the Risk Management Plan” (p. 68). Thus, the agenda for the risk workshop on the problems of Flayton Electronics will include the following.
A workshop should begin with an introduction to greet the stakeholders. The following presentation of the project’s background is aimed at getting the participants acquainted with the problem. The analysis of the objectives is going to clear up the purpose of the meeting. Presentation and explanation of the risk management process for Flayton Electronics present specific features of risk management in the company. It is also important to identify the expected results and their influence on the implementation of the project. The first part of the workshop finishes with risks identification and the following brainstorming of the identified risks to create the strategies able to prevent the identified risks.
The second part of the workshop includes the analysis of assumptions and constraints for the risk management of the company. It is followed by an important stage of defining the possible risks that demands the application of a checklist. The first day finishes with the identification of initial risk responses that are necessary because they can be further developed into real actions. Finally, the records of the identified risks should be done to create the basis for further work during the second day of the workshop.
During the second day, it is necessary to rationalize the risks and reveal duplicates or risks that will not have any significant impact on the project. It is important to provide clear and unambiguous description of all identified risks to make this information available and explicit for the stakeholders not present in the workshop. Moreover, appropriate description would allow to develop the risk categories. It is a necessary step because categorization helps to manage the risks more efficiently. After all, the responsible stakeholders should be defined and the possible risk-prevention interventions have to be developed. Finally, the conclusions are drawn and the workshop is closing.
Top Threats and Opportunities
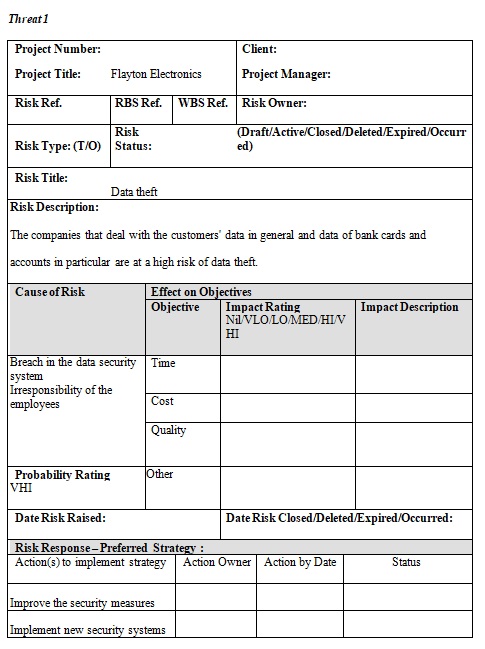
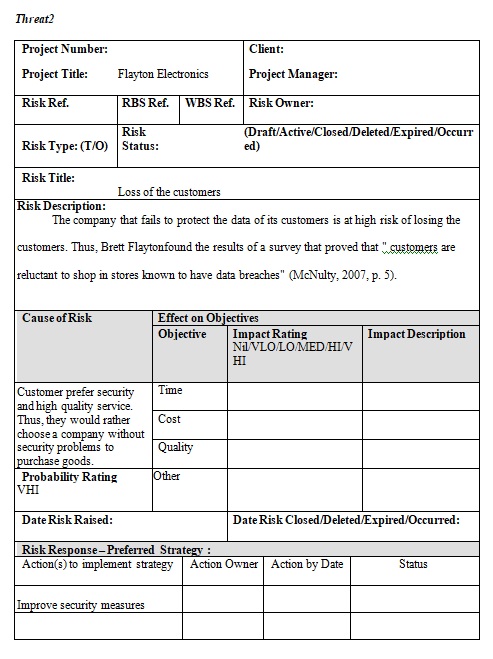
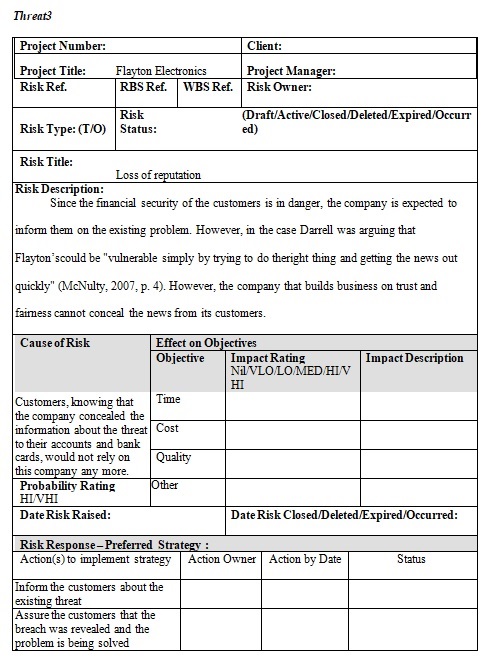
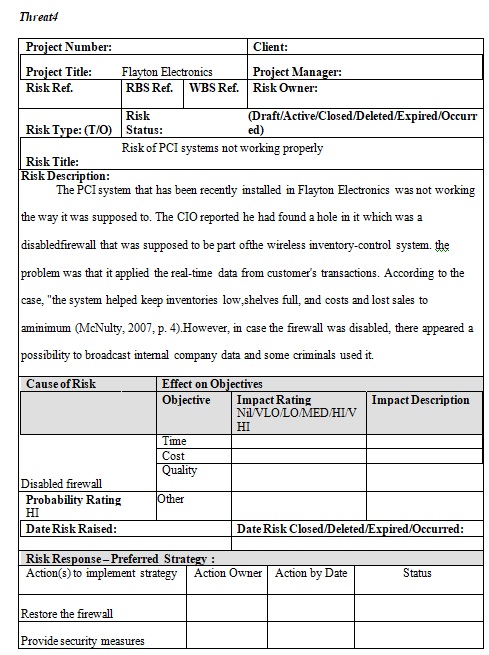
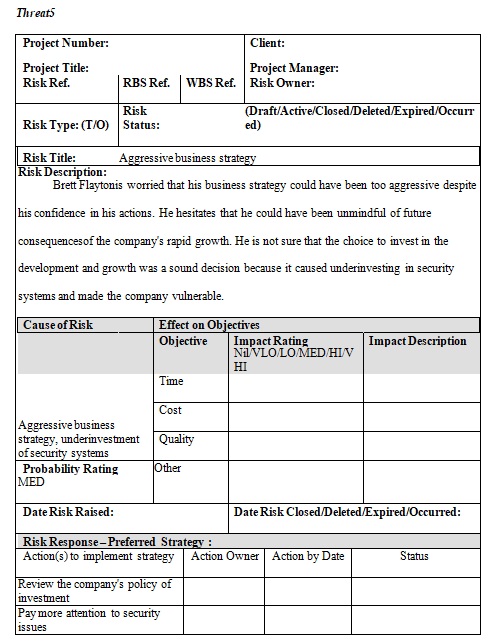
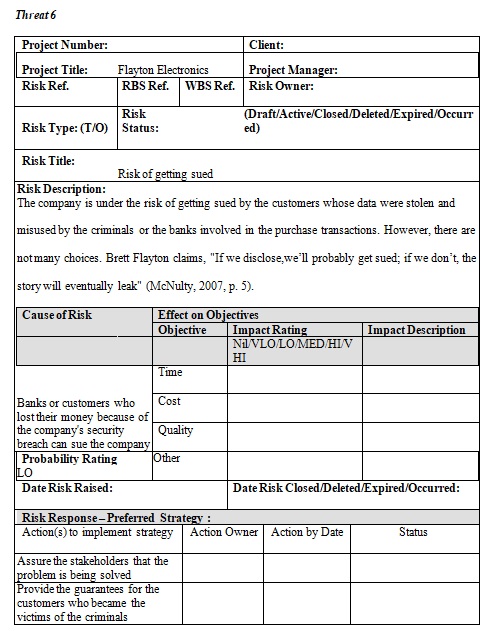
Threats
Opportunities
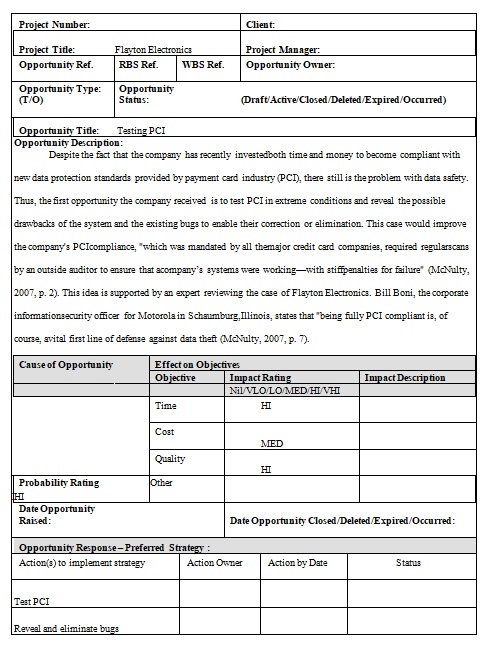
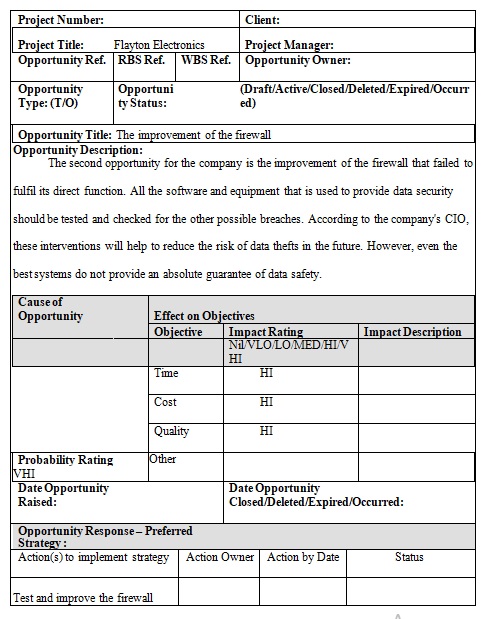
Despite the existing threats and risks for Flayton Electronics, the company got some opportunities for development and improvement. They should be considered to provide business continuity and manage the possible risks (Graham & Kaye, 2015).
Opportunity 1
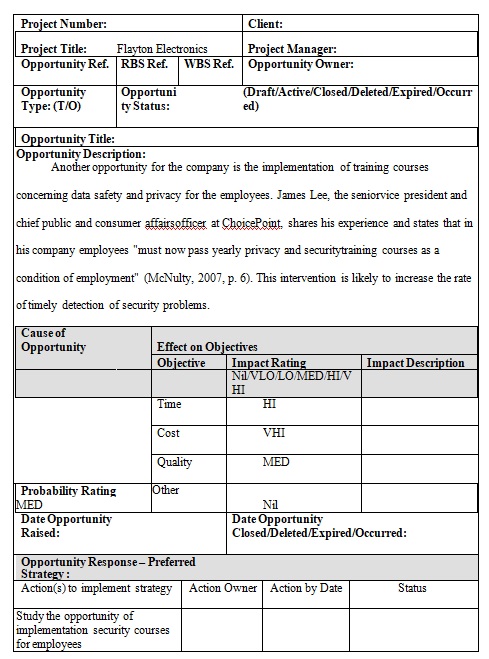
Opportunity 2
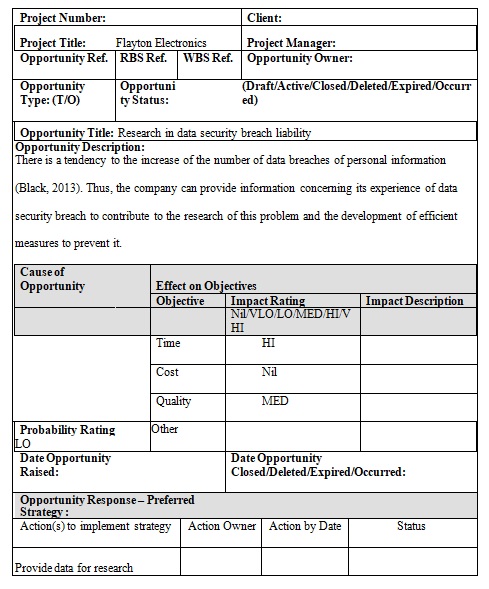
Opportunity 3
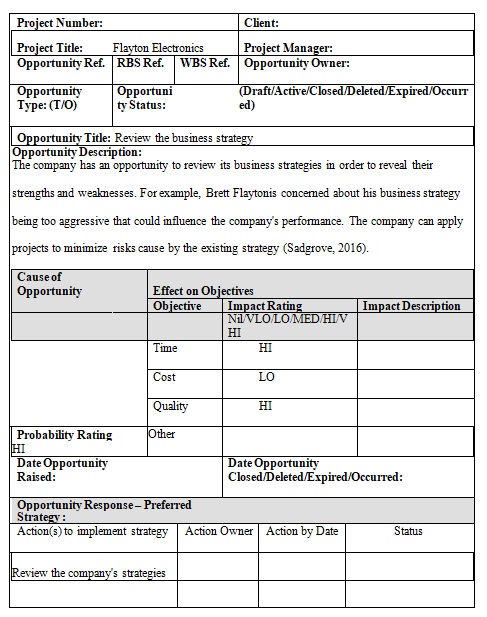
Opportunity 4
Opportunity 5
Conclusion
On the whole, the process of identifying the risks is complicated. However, it is a necessary part of any business because it helps to reveal the risks of different probability and manage them accordingly which is likely to reduce the harm of those risks to this or that project. Risk register is one of the methods to control the risks and manage them. It is usually created as a result of a risk workshop that gathers all stakeholders involved in the spheres with high risk probability. Timely definition and registry of risks are steps to their proper management and, finally, leads to better performance of the company.
References
Black, J. (2013). Developments in data security breach liability. The Business Lawyer, 69, 199-207.
Danesh-Mand, P. (2015). Some tips to facilitate a successful risk workshop. Web.
Graham, J., & Kaye, D. (2015). A risk management approach to business continuity. Brookfield, CN: Rothstein Publishing.
Hillson, D., & Simon, P. (2012). Practical project risk management (2nd ed.). Tysons Corner, VA.: Management Concepts.
McNulty, E. (2007). Boss, I think someone stole our customer data. In Harvard business review (p. 1-11). Boston, MA: Harvard Business School Publishing.
Sadgrove, K. (2016). The complete guide to business risk management. New York, NY: Routledge.
